This week I faced an interesting problem with my setup based upon the following components:
- Proxmox run on Custom Hardware
- Home Assistant installed within a VM
- Frigate runs within Home Assistant as Add-On
- Home Assistant uses for this AFAIK Docker
- Coral TPU is configured within the Host
- Frigate runs within Home Assistant as Add-On
- JetKVM
The problem was, that the JetKVM together with the Coral TPU drawn too much power from the USB Port, so that the Firgate Add-On often ended up with the following loop within the log:
INFO : Detection appears to be stuck. Restarting detection process...
INFO : Waiting for detection process to exit gracefully...
INFO : Detection process didn't exit. Force killing...
INFO : Detection process has exited...
INFO : Starting detection process: 1223
INFO : Attempting to load TPU as usb
INFO : TPU foundThis blog does not provide more infomration than what was already stated
Proxmox and Coral TPU
To install the Coral TPU within proxmox, to make it available to Home Assistant, I followed this blog:
https://homeiac.github.io/home/md/proxmox_guides_google-coral-tpu-frigate-integration.html
The exception is the download of the Edge TPU runtime, which you can find within this website:
https://coral.ai/software/#edgetpu-runtime
JetKVM
I have recently installed my JetKVM (https://www.kickstarter.com/projects/jetkvm/jetkvm), also with a very nice usage for the 5,25” Slot of my case with the following model:
https://www.printables.com/model/1142190-jetkvm-525-mount
This does also draw power from the USB, which apparently together with the Coral TPU draws too much energy from my mainboard. This was the change my System was undergoing, and afterwards the loop mentioned earlier is found in the log, and frigate stops working due to the missing TPU.
Troubleshooting steps
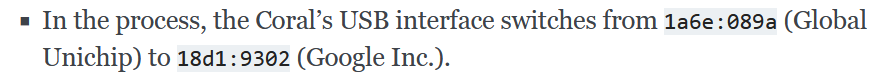
Beside the very helpful information about the Hardware IDs on the mentioned blog:
The following GitHub Issue also pointed me in the right direction:
https://github.com/blakeblackshear/frigate/issues/3966